In today’s interconnected world, remote access has become a necessity for many organizations, allowing employees to work from anywhere with a network connection.
However, this convenience also introduces security risks that must be addressed to safeguard sensitive data and maintain network integrity.
Strengthening your network defense when it comes to remote access is crucial, which is why this article will explore key strategies and best practices to enhance remote access security and protect your organization from potential threats.
Use Secure Remote Access Technologies

One of the best things you can do to start with is implement secure remote access technologies, such as Virtual Private Networks (VPNs) and Remote Desktop Protocol (RDP) gateways.
VPNs create an encrypted tunnel between remote devices and your network, ensuring that data transmitted over public networks remain secure, while RDP gateways provide a secure intermediary for remote desktop connections, adding an extra layer of authentication and encryption to make certain that your data is safe.
Implement Access Controls
Utilize access controls to restrict remote access privileges. One of the best ways to ensure that you can effectively control the flow of authorized access into your network is by making use of one of the many high-quality Firewalls available to businesses in the modern market.
Using a firewall to control IP access, you can ensure that you grant access only to authorized users who require it for their roles. Plus, utilizing a tool like this allows you to regularly review and update access permissions to ensure that former employees or contractors no longer have access to your network.
Be sure to keep the principle of least privilege in mind as you engage with allowing and removing access to your network.
Enforce Strong Authentication
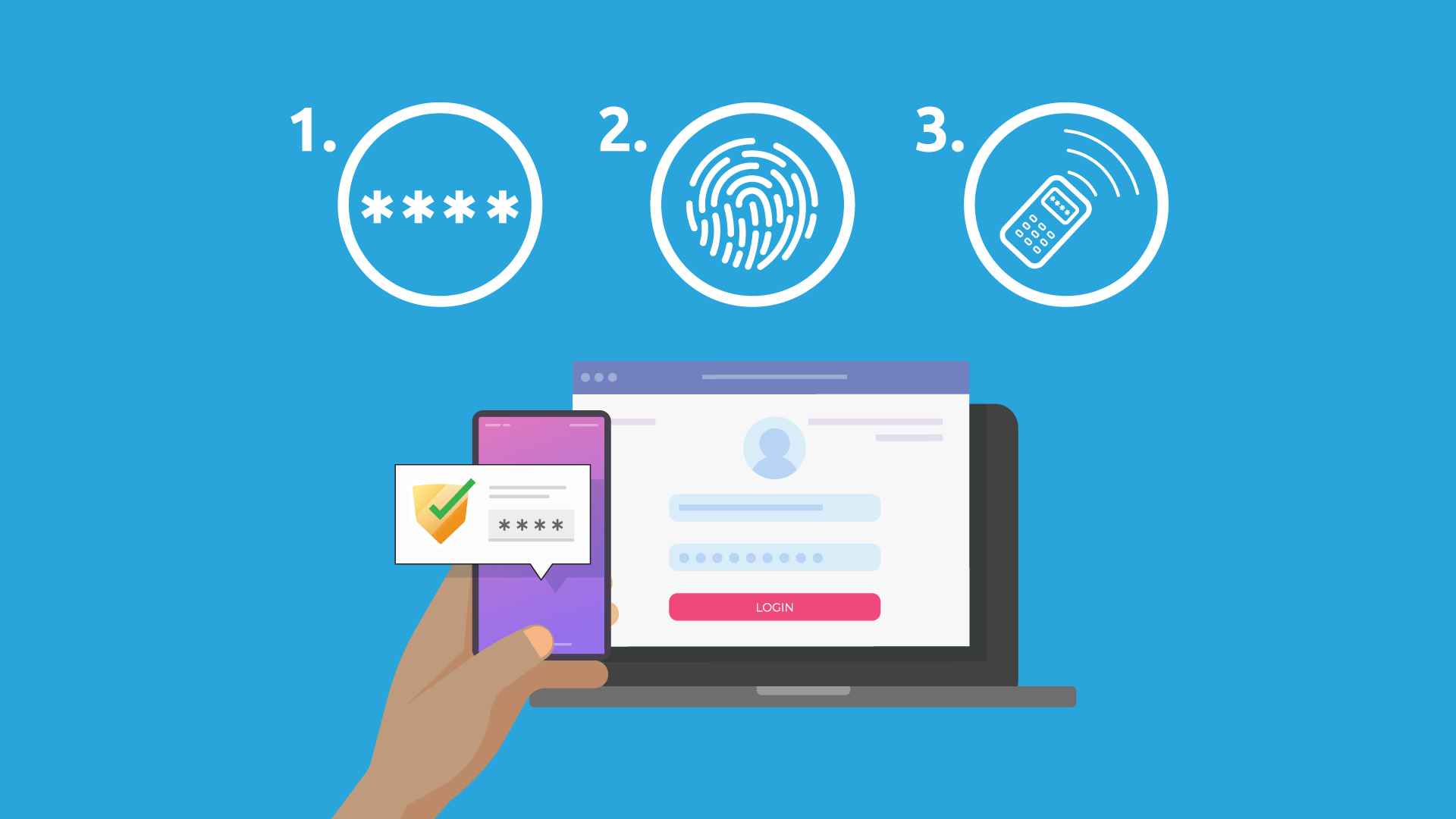
Once you have both secure remote access set up and a strong firewall to manage access to your network, you might also want to consider the benefits of adopting strong authentication methods for your employees.
For example, you could implement multi-factor authentication (MFA) to require additional verification beyond a username and password, which can help to ensure that only your employees can access their accounts – even if someone else gains access to their sign-in information.
Often the best options for this is to opt for an MFA that sends a one-time passcode via SMS or authenticator apps, as this means that your employees’ phone is also required to enable access, which massively reduces the chance of another person using their account.
Conduct Regular Security Assessments

Perform regular security assessments to identify vulnerabilities and weaknesses in your remote access infrastructure. Be sure to contact your remote working employees to identify any particular points for improvement. After all, working directly with your employees allows you to benefit from their direct experience with the system.
Create an Incident Response Plan
Finally, you might want to develop a comprehensive incident response plan specifically tailored to remote access security incidents. Define roles, responsibilities, and procedures for responding to security breaches.
Establish clear communication channels and escalation processes to ensure that every one of your employees knows exactly what to do in such a situation.
Of course, once you’ve set up a system like this it is incredibly important that you regularly test the system to make sure that it works as intended and doesn’t fall short in any particular regard.






